1 Introduction / Executive Summary
The cyber threat landscape that businesses, non-profits, and government agencies face today continues to evolve at an alarming pace, challenging cybersecurity staff and solutions to stay a step ahead of adversaries. As the realm of cyber threats expands, organizations have the difficult task of managing their attack surfaces effectively to protect their valuable assets. Attack surface management (ASM) has emerged as a crucial discipline that enables proactive cybersecurity strategies, mitigating risks by reducing an organization's exposure to potential attacks. CISOs are increasingly looking for portfolio consolidation opportunities, and ASM solutions provide the opportunity to centralize some functions that organizations are doing themselves as well as some functions that have been outsourced to service providers.
The attack surface is defined as the totality of all possible entry points within an organization, as well as the digital infrastructure of its subsidiaries and partners. It includes the hardware, software, storage, networks (on-premises and cloud), and identities (of users, service accounts, and devices) that attackers can exploit to deny service, gain unauthorized access, launch attacks, or compromise sensitive data. The attack surface is always changing, as the elements that compose it are themselves continually in flux, which means that round-the-clock monitoring and assessment is needed for due diligence.
ASM can play an important role in modern cybersecurity, enabling organizations to identify, analyze, and mitigate potential attack vectors effectively. As a discipline, ASM takes the attackers’ point of view. In fact, some vendors describe their ASM services as continuous red teaming. By gaining visibility into their attack surfaces as hackers perceive them, security teams can proactively defend against emerging threats, reduce vulnerabilities, and enhance incident response capabilities. IT security teams often lack an effective way to communicate risks about security vulnerabilities to business teams and IT asset owners. ASM solutions can enumerate vulnerabilities, analyze exposure, and combine business context and risk information in a way that is easier to consume and more actionable than previous methods.
ASM can enable deploying organizations to adopt a risk-based approach, allocating resources strategically to areas with the highest potential for compromise.
ASM solutions generally perform the following functions, and ideally in a continuous or frequent fashion:
- Asset Discovery: Enumeration and identification of all elements that constitute the attack surface, including hardware assets, networks, applications, cloud resources (both SaaS and IaaS), and external dependencies such as identity federations, collaborative applications, shared accounts, etc. Many organizations need detailed software discovery and Software Bill of Materials (SBOM) information to comply with government directives and regulations, such as the US National Telecommunications and Information Administration’ guidance for US Executive Order 14028. Asset discovery may use both passive and active modes. Some of the solutions on the market today rely on third-party tools for asset discovery and classification.
- Asset Profiling and Vulnerability Assessment: Profiling is the process of acquiring detailed information about each component within the attack surface, such as hardware/firmware/software version information, configuration settings, and overall exposure to threats to create profiles for each asset. Vulnerability assessment involves using various techniques such as dedicated scanning for Common Vulnerabilities and Exposures (CVEs), identifying software and operating system misconfigurations, and penetration testing to evaluate the resilience and/or susceptibility of the attack surface and to identify potential attack vectors. Analysis of data obtained from the profiling and assessment activities can be facilitated by machine learning (ML) algorithms. Some of the solutions on the market today rely on third-party tools for vulnerability assessment and management.
- Prioritization: Information from the ongoing assessments can and should be risk-scored per asset and contextualized. Most vendor implementations align with the NIST Common Vulnerability Scoring System (CVSS). Some also recognize and implement the Forum of Incident Response and Security Teams’ Exploit Prediction Scoring System and aggregate these risk and prediction scores to determine the best order for addressing risky assets. Sometimes vulnerabilities marked as critical may not be the highest risk, depending on customer exposure and business context; therefore, those vulnerabilities may receive a lower risk rating. This helps security teams more effectively prioritize remediation efforts based on risk severity, specific customer asset exposure, potential impact, and available resources. Determining priorities for action is an essential built-in function for ASM solutions.
- Monitoring: Regular monitoring is essential to detect changes in the attack surface, new vulnerabilities, and emerging threats. This stage requires facilities to detect changes in customer environments, real-time cyber threat intelligence (CTI), log and telemetry analysis, and analysis of security event information. Monitoring and reporting are key functions of all ASM solutions. Most vendors perform the various scanning operations described above either manually (on-demand), periodically, or continuously. Monitoring also provides status of remediation actions.
- Remediation: This stage involves implementing new or enhancing existing security controls and configurations to reduce vulnerabilities and shrink the attack surface. This is typically done by recommending and/or executing the application of patches and firmware updates, operating system and application patches, configuration changes, and other measures. Most ASM solutions rely on third-party systems to effect changes, which requires application programming interface (API) connectivity and often customization. The most common remediation support is in the form of providing detailed guidance on how to manage vulnerabilities, patch apps and operating systems (OSes), limit access, and properly configure apps and OSes.
To meet the challenges of the evolving threat landscape, ASM vendors offer innovative tools that address the following functional areas:
- Attack Surface Reduction: Organizations can implement attack surface reduction techniques such as implementing zero trust architecture (ZTA), which includes enforcing the principle of least privilege, strong authentication and fine-grained authorization, and network segmentation to limit the exposure of and risk to assets. Interoperability with other security tools is needed for effective attack surface reduction.
- Attack Surface Visualization: Advanced visualization techniques provide an intuitive view of the attack surface, allowing security analysts and architects to understand their complex infrastructures and find previously unknown vulnerabilities. Visualizations should show all assets, CVEs and other types of vulnerabilities, and risks in a logical format, with mappings to MITRE ATT&CKÒ. Most ASM tools have adequate (or better) visualization capabilities. The ability to integrate information from ASM platforms into other tools is, on the whole, less well-developed at present, due to a lack of connectors and/or insufficient API exposure in some vendor implementations.
- CTI Integration: By directly incorporating cyber threat intelligence feeds into ASM solutions, security teams can enhance their understanding of potential threats and prioritize remediation efforts based on up-to-date CTI. Most ASM vendors have their own in-network CTI sources (often originating from internal threat research and ethical hacker teams), while some also integrate with third-party or open-source CTI feeds.
- Automated Attack Surface Management: Automation can be an important part of ASM solutions, enabling ongoing asset and vulnerability discovery, profiling, and monitoring of the attack surface. Automation is highly desirable in order to increase the efficiency of security teams. Automation services vary substantially from vendor to vendor.
- Attack Surface Analytics: Leveraging data analytics and ML algorithms, ASM solutions can analyze large amounts of data from various sources to help deploying organizations better understand their attack surface. This facilitates the recognition of patterns and detection of anomalies and can lead to better decision-making regarding both tactics and strategic investments for security tools.
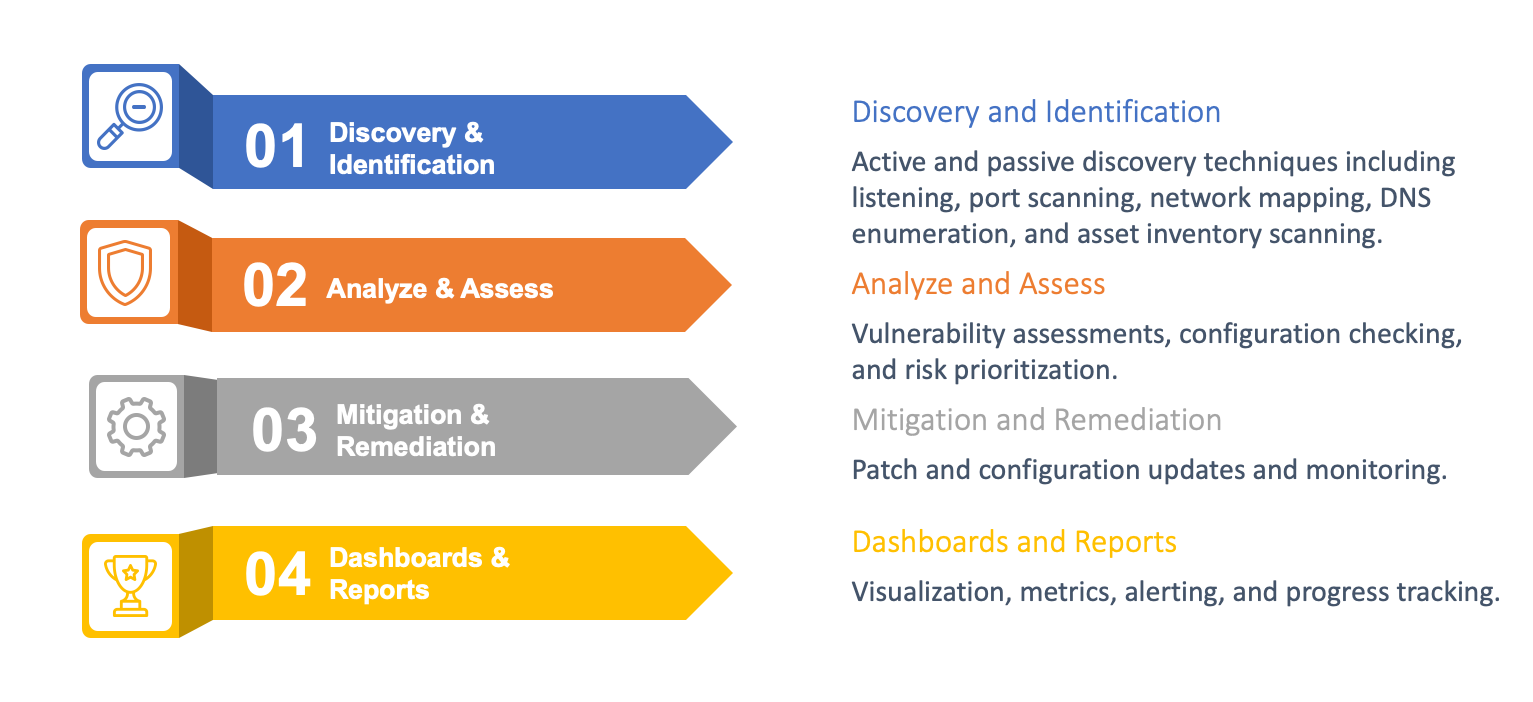
Figure 1: Key Functions of ASM
ASM can be a vital part in an overall enterprise risk management strategy. By effectively monitoring and reducing the attack surface, organizations can minimize their overall risk exposure and improve their resilience against cyberattacks. IT security teams may engage ASM services, but they are often not the owners of the systems that are found to need remediation. Thus, security teams must work with IT operations, development teams, business units, and executive management to ensure a comprehensive understanding of the attack surface and implement effective security measures.
ASM is an emerging and dynamic discipline. Here are some key areas of evolution in attack surface management:
Cloud (SaaS and IaaS): The widespread adoption of cloud computing has significantly expanded the attack surface. Almost every organization, large and small, makes use of SaaS applications today. Many enterprises use IaaS, and if not solely IaaS, then in hybrid mode with on-premises assets as well. Attack surface management must be able to discover, assess, and monitor resources hosted in these environments, as well as operate in and understand cloud-based architectural features such as elastic scaling, shared responsibility models, containerized applications, and shadow IT. All ASM solutions today are cloud-hosted, and the vendors are focused on external web and cloud threats.
Internet of Things (IoT): The proliferation of IoT devices and their various uses by enterprises increase risk and lead to new complexities in terms of attack surface management. Security teams and the tools they rely on must consider IoT vulnerabilities and the potential impact on the overall attack surface. This is an area of specialization that not all vendors address currently.
Dark Web Monitoring: Innovative ASM vendors have infiltrated dark web sites, ransomware-as-a-service sites, APT groups, instant messaging groups, discussion forums, and information exchanges. This enables them to find evidence of past successful attacks such as leaked information from data breaches, including companies’ proprietary information and individuals’ personally identifiable information (PII). ASM vendor researchers also may find compromised credentials, zero-day malware, insufficiently protected remotely controllable assets, and credit card and other account information for sale. Dark web monitoring can also give these ASM vendors advance notice of potential attacks and their targets, which they can then pass on to their customers.
Brand Protection: The features in ASM platforms for brand protection may include looking for signs of disinformation campaigns, social media reconnaissance, DNS manipulation, typosquatting, website spoofing, impersonation, and phishing. These functions are a subset of the broader category of brand protection, which also includes monitoring for improper or illegal use of logos, text, and media; social media manipulation; piracy, grey market sales, and counterfeit products; fake websites and fake or compromised mobile apps; etc.
DevSecOps Integration: Security must be integrated into the DevOps workflow. By incorporating security practices early in the development lifecycle, organizations can proactively address vulnerabilities and minimize the attack surface from the start. Many ASM vendors offer application security testing services in addition to their main solutions. Since most ASM vendors are focused on internet-facing assets, those particular solutions may not be suitable for applications intended for traditional intranet use.
Threat Modeling and Attack Simulation: Advanced threat modeling techniques and attack simulations provide valuable insights into potential attack vectors and their impact on the attack surface. These proactive approaches help organizations identify and remediate vulnerabilities before they can be exploited by adversaries. ASM solutions can aid in threat modeling exercises. The related field of breach and attack simulation (BAS) is still distinct from, and not generally a part of, most commercial ASM products and services today. We expect ASM and BAS to come together in more comprehensive offerings in future.
Regulatory Compliance: Most organizations are subject to one or more regulations, depending on the type of enterprise and the jurisdictions in which they operate. Privacy regulations such as the EU General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA) have garnered much attention in recent years. Other regulations in industries such as banking, finance, payments processing, insurance, healthcare, manufacturing, energy production, oil and gas, aerospace, etc., mandate specific security measures. Compliance requirements can directly and/or indirectly require organizations to have a clear understanding of their attack surface and implement measures to protect sensitive data governed by pertinent regulations. Some of the solutions analyzed in this report have compliance modules that are designed to help customers measure and report on compliance with specific regulations or frameworks.
This KuppingerCole Leadership Compass provides an overview of vendors and their product or service offerings in the ASM market.
Highlights
- Attack Surface Management (ASM) is an emerging but not fully mature discipline and technical solution type within the broader field of cybersecurity.
- ASM is composed of two main branches currently, external ASM (EASM) and cyber asset ASM (CAASM). CAASM is more internally focused.
- Asset discovery, vulnerability assessment, risk scoring, and prioritization, reporting, and remediation are the primary functions of an ASM system.
- Not all ASM vendors have fully in-house developed components; many rely on third-party products for some key functionality.
- Integrations with other security and IT tools, as detailed below, are essential for enabling ASM tools to maximize their utility in customer engagements
- Dark web monitoring is a set of techniques and practices that many ASM vendors employ for threat research and discovering client specific threat information.
- Some vendors offer manual and/or automated penetration and red teaming services.
- Some vendors offer limited brand protection features.
- EASM and CAASM will merge as deploying organizations seek to combine internal and external attack surface management in a single solution.
1.1 Market Segment
The Attack Surface Management market has emerged in the past few years with antecedents in asset management, vulnerability management, penetration testing, red teaming, cyber test ranges, and, to a lesser degree, BAS. ASM combines many of these techniques, and in many cases automates these techniques, to deliver a more frequent and cost-effective set of related security capabilities. Vendor solutions in the ASM market are maturing. There is a wide array of possible features available in the products and services in the market today. At present, most vendor solutions are focused on external ASM, or EASM: what can be tested and assessed from outside customer organizations’ infrastructure. A broader view of ASM is reflected in the market definition for this research in which ASM solutions are defined as those designed to address cyber threats stemming from organizations’ ever-growing attack surface. The overall attack surface for organizations is made up of two distinct parts:
Digital Attack Surface: operating systems, applications, websites, APIs, virtual machines (VMs), containers, cloud-hosted services, code, shadow IT, etc.
Physical Attack Surface: workstations, laptops, servers, mobile phones, hard and USB drives, IoT devices, operational technology (OT) and industrial control systems (ICS) components, etc.
We believe that the ASM market will move toward this more complete definition, including covering internal and physical assets like the CAASM market. This would require the availability of on-premises components, such as appliances (physical or virtual) or installable agents for endpoints. The EASM and CAASM functionality split is not likely to be tolerated by enterprise buyers of ASM products and services indefinitely.
The ASM market today is already quite large and diverse, with both large and small, and established and startup vendors present. We expect this market to continue to evolve, mature, and grow.
ASM, therefore, can benefit many types of organizations, but given that feature sets in current examined offerings are primarily aimed at external ASM, those with extensive web estates and customer-facing infrastructure will see the most value. Each solution evaluated has different strengths that will appeal to different organizations, depending on their particular requirements.